سجل المستندات التعريفية
بحث
المستندات المتاحة حاليًا: 11532
أحدث الموضوعات:
The Ultimate Guide To The OWASP 21 Top Automated Threats and Security Capabilities To Stop Them
عرض المستندات التعريفية
Challenges in Application Security (And Why Your On-Prem WAF is No Longer Enough)
عرض المستندات التعريفية
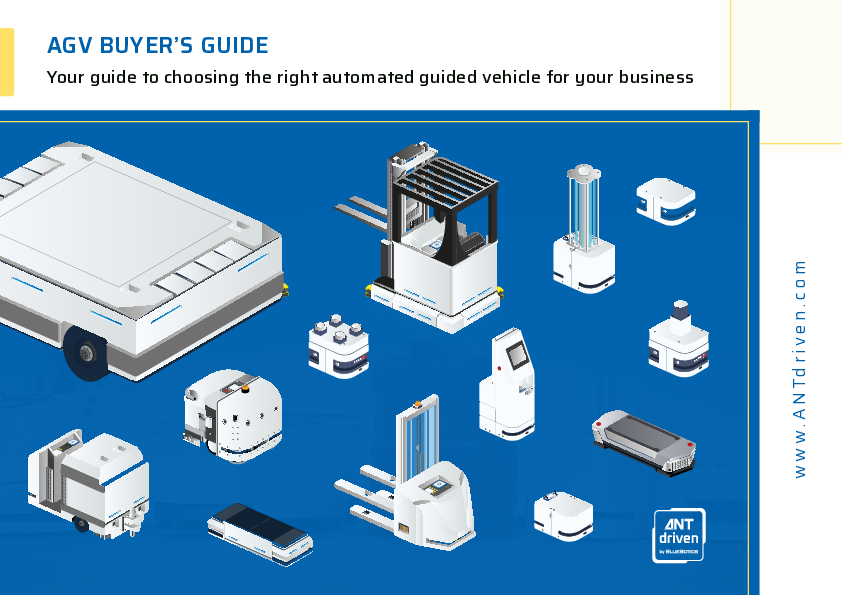
AGV BUYER’S GUIDE: Your guide to choosing the right automated guided vehicle for your business
عرض الكتاب الإلكتروني
Achieving Operational Excellence within your Laboratory via Integrated Digital Solutions
مشاهدة الفيديو
Stay Ahead of Year End Overload: Streamline Reporting With Automated Disclosures
مشاهدة ندوة على حسب الطلب عبر الإنترنت
سجل في نشرتنا الإخبارية
تلقى أهم الأخبار عبر البريد الإلكتروني مجانًا