Whitepaper archive
Search
currently available documents: 11530
Latest topics:
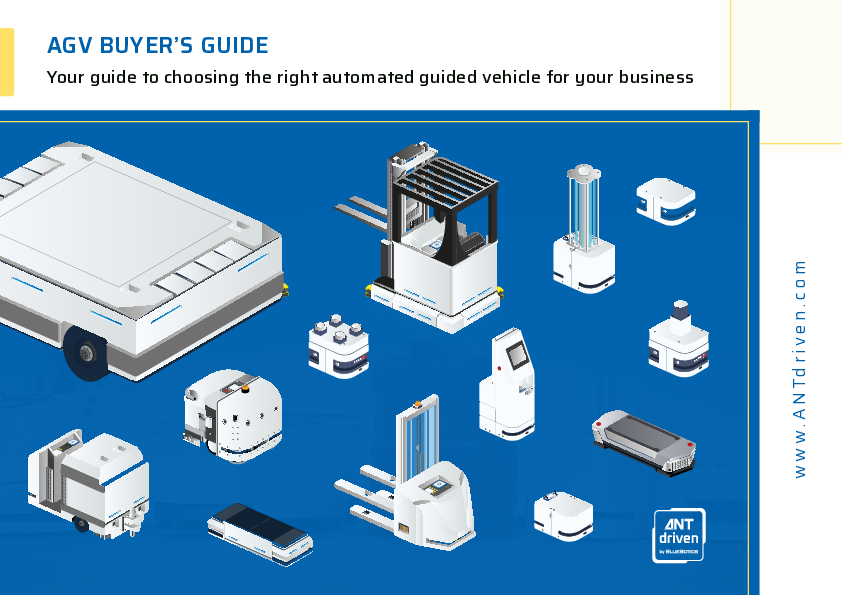
AGV BUYER’S GUIDE: Your guide to choosing the right automated guided vehicle for your business
View eBook
Achieving Operational Excellence within your Laboratory via Integrated Digital Solutions
Watch the video
Stay Ahead of Year End Overload: Streamline Reporting With Automated Disclosures
Watch the On-Demand webinar
Register for our newsletter
The most important news for free via E-Mail